Putting a mailto: link on your website is the easieiest way for a web user to get ahold of you. It requires only a single click on a hyperlink on their part to open their email client, address the email, insert a subject line, and pre-fill the body of the document… and it utilizes the standard email mechanisms out there to record thier email address, server, and path the message took to get to you. It’s also a breeze to impliment.
The downside, this also allows spambots to harvest your email address easily.
There are many ways to obfuscate your email address. Most of which make things more difficult for you to impliment and/or maintain, or more difficult for your web users to use. The former is an inconvenience at best, the latter is suicide (in a business context).
After looking at javascript solutions, PHP solutions, ASPx solutions, CSS2 solutions, CSS1 solutions, and graphical solutions, this seems to be the best that I’ve come across.
Basically, this method encodes the entire mailto: string, making things easy for the browser to interpret, but adds a layer of difficulty to the spambots.
True, it’s only a layer of difficulty, but if your sole purpose is to harvest as many email addresses as possible in the shortest amount of time, the extra time that it takes to develop and run your spambot means less money for you. So the greedy buggers are probably going to let it slide.
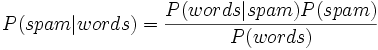 Even if they don’t, hopefully they’ll think rationally about the type of users that are going to lengths to obfuscate their email address: that type of user probably has a Bayesian Filter, blacklist, whitelist, or challenge-based system set up to limit the spam they’re exposed to. In other words, the obfuscators are the people that the spambot authors don’t want to include in their lists because they (the obfuscators) probably won’t see the email anyway.
Even if they don’t, hopefully they’ll think rationally about the type of users that are going to lengths to obfuscate their email address: that type of user probably has a Bayesian Filter, blacklist, whitelist, or challenge-based system set up to limit the spam they’re exposed to. In other words, the obfuscators are the people that the spambot authors don’t want to include in their lists because they (the obfuscators) probably won’t see the email anyway.
Via Colmgallagher.com.





Thanks for the heads up. I’ve now changed my mailto: links on my website.
I still have one or two lingering around… I figure between this and a “challenge” based spam filter, one ought to be 90+% covered. 🙂